As we enter 2024, stolen and leaked credentials continue to be a leading cause for compromised accounts. This is often down to Social Engineering such as phishing, business email compromise (BEC) and 3rd party breaches. To mitigate this, businesses and vendors alike are rolling out multi–factor (MFA) authentication to their SaaS and on-premise applications. This is often in the form of One-Time passwords (OTP), and push notifications via MFA apps on smartphones, the latter being preferred, and often seen as the more secure method.
Cyber criminals, adversaries and online nuisances are now having to get creative to circumvent this new defensive edge businesses are deploying. The attack technique I will be talking about today is known as ’Multi-Factor Authentication Request Generation – Mitre T1621’. This is where adversaries in the possession of a person’s credentials will repeatedly attempt to login in order to bombard them with MFA push notifications until they press accept/allow. Essentially the user is spammed with repeat notifications until they press accept, allowing them to gain access. Often this is done in the early hours of the morning to catch the victim off guard. I think we can all admit we have pressed accept on a notification on our phone without properly checking it. And that’s all it takes, a lapse in concentration and a hacker has access to your account.
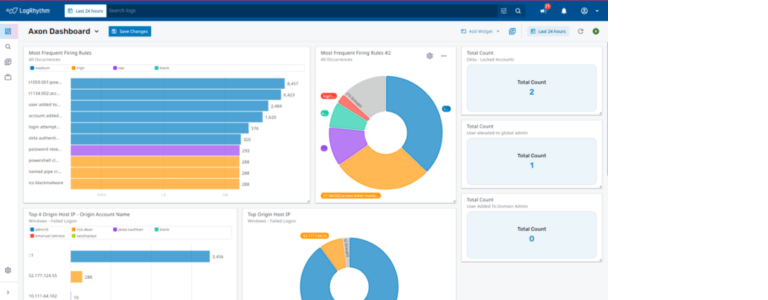
Detecting this type of attack can often be difficult, especially when only using the tools built into the Identity Provider (IDP). This is where LogRhythm Axon comes in. LogRhythm Axon is a cloud-native Security Information and Event Management platform (SIEM), designed and built for use cases just like the one we are discussing. Axon has a long list of integrations and supports multiple cloud and on-premise log source types, allowing comprehensive visibility into a customer’s tech stack to find threats faster and ultimately stop them in their tracks.
Connecting Axon to an IDP such as Okta can be done with relative ease, and it’s done leveraging Axon’s collectors and APIs. From experience, it often takes no longer than 30 minutes to get logs from an Okta environment into Axon. And as an added bonus, when all the logs land in Axon they are readable and usable from day one!
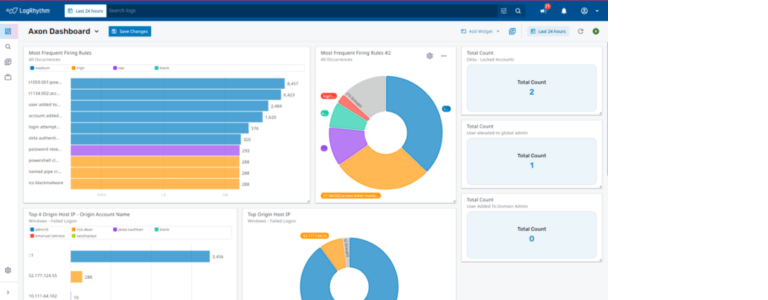
Let’s circle back to MFA requested generation. Axon offers an arsenal of Mitre aligned threat detections out-of-the-box, T1621 being one of them, making it a lot easier and more likely to detect this type of attack on the network. Importantly Axon provides analysts with the ability to build bespoke threat detection rules within the platform by creating observational rules suited to their own environments.

To summarise, using conditional access, user access policies and/or phishing resistant MFA can be a way to mitigate this type of attack, but Axon can be on hand for detection capabilities and provides analysts with the ability to complete their investigations seamlessly and easily.