Censys
Data-driven Attack Surface Management
No surprises, only actionable insights.

Continuous Threat Intelligence
Censys is a data-driven security platform which provides users with real-time attack surface discovery. It automates finding digital vulnerabilities while providing continuous threat intelligence to remediate future risks. Their industry-leading internet scanning platform and >9.1B certificate database (the world’s largest) – enables them to provide 63% more coverage than their nearest competitor. Ensuring governance over your customer’s cloud adoption.
Censys Attack Surface Management Capabilities
Censys ASM discovers 85% more services than the nearest competitor.

Discover
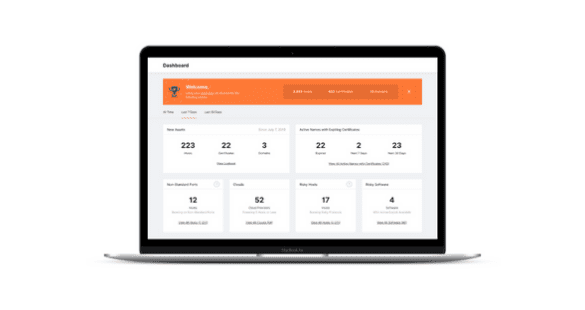
Organisations can discover unknown and unmanaged internet-facing assets — including services, hosts, websites, storage buckets, and cloud accounts — across all cloud providers and networks (AWS, Azure and GCP) in real-time.

Identify
Censys provides risk-based detection for over 120 different types of internet assets and identifies weaknesses and misconfigurations – with recommendations to remediate or eliminate threats.

Maintain
Multi-national organisations with large digital footprints can maintain a comprehensive inventory of all their internet assets and configurations, as well as a logbook of activity to track changes to their attack surface.
Integrates Seamlessly With
Why Your Customers Need Attack Surface Management
Attack surface management (ASM) helps your customers build a comprehensive inventory of all their internet assets – to ensure they have not been misconfigured to prevent unauthorised access. Gartner recommends that security and risk management leaders should “anticipate the continuous expansion of the enterprise attack surface, and increase investment in processes and tools for identity threat detection and remediation and digital supply chain integrity.” With 60% of knowledge workers working remotely, organisations must acknowledge the risks associated with modern work practices.
Censys Data & Search Use Cases
Enhanced Threat Intelligence
Improves threat intelligence operations, enabling better and more accurate pivots off of known IoCs and learning when infrastructure was weaponised by the adversary through historical data lookup.
Vulnerability Research
Identifies specific software vulnerabilities on assets connected to the internet like SolarWinds or Microsoft Exchange, and gain a global perspective of potential impact.
OSINT for Red and Blue Teams
Conducts reconnaissance in red teaming exercises or leverage Censys Data as a blue teamer to find hosts running services exposed to the Internet, even services running on non-standard ports.
Case Studies
Finance
Swiss Life provides financial security for individuals and corporations. As the organisation is divided into several divisions, it faced challenges with visibility into the governance and compliance issues its security teams were finding.
Immediately after Censys’ initial internet-wide scan, Swiss Life’s security leaders were able to see their internet assets and prioritised risks all in one place within its dashboard. This helped Swiss Life remain efficient and compliant.
Real Estate
A public real estate company with over 50,000 employees, a lean security team and multiple subsidiaries were struggling to manage and patch its internet assets.
Censys’ cloud asset discovery algorithm identified 18 storage buckets that were unknowingly leaking public data and more than 600 cloud assets outside of monitored accounts. It also revealed 60 new risks on previously unknown assets, including deprecated protocols, protocol misconfigurations, and vulnerable end-of-life software.
Trusted By
Request Your Demo
Ready when you are! Take a quick demo with one of our experts and learn why…


















