The World’s Leading Security Key to
Strong Enterprise Authentication
Yubico sets new global standards for simple and secure access to computers, servers, and internet accounts. The company’s core invention, the YubiKey, delivers strong hardware protection, with a simple touch, across any number of IT systems and online services. The YubiHSM, Yubico’s ultra-portable hardware security module, protects sensitive data inside standard servers.
Not All MFA Is Created Equal
More than 70% of breaches exploit stolen credentials. Multi-factor authentication (MFA) should be a first-line defence of any cybersecurity strategy. But not all forms of MFA are created equal. Legacy MFA such as SMS, OTP and push notification apps don’t stop modern cyber threats. Modern, phishing-resistant MFA, offered only by FIDO or Smart Card/PIV protocols, have been proven to stop account takeovers in their tracks.
Hardware security keys, such as the YubiKey, support multiple authentication protocols including FIDO U2F, FIDO2, and Smart Card/PIV, making them truly phishing-resistant and delivering peace of mind.

Bridge to Passwordless
Seven Steps to Execute a Smooth Passwordless Implementation
There are as many definitions of passwordless as there are passwords. While it’s widely recognised that there are many benefits to achieving secure account login without the use of passwords – going passwordless can be a confusing topic.
Yubico have have perfectly summarised these easy seven steps which will help every enterprise whether they have a particular focus on their current user environment, their existing authentication processes or their IT staff are ready to cross the bridge to passwordless.
Webinar Library
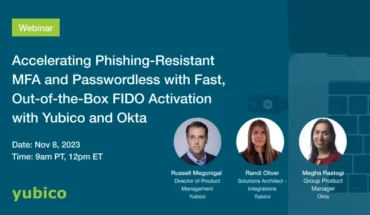
Fast, Out-of-the-Box FIDO Activation With Yubico and Okta
Learn more about the approach of “Accelerating Phishing-Resistant MFA and Passwordless with Fast, Out-of-the-Box FIDO Activation with Okta.”
Many Roads to Passwordless: How Passkeys Fit in the Modern Landscape
Passkeys are the long awaited replacement for passwords. Come learn how passkeys help accelerate widespread adoption of passwordless authentication for consumers and organisations.
Let's find the right YubiKey for you
The YubiKey comes in a variety of sizes and shapes to suit all devices and operating systems! This quick quiz will help you discover which YubiKey best suits your needs.
Okta Adaptive MFA and YubiKey Deliver Strong and Scalable Phishing-Resistant Authentication Solutions
Create intelligent policies that adapt the level of identity assurance all the way up to hardware-based authentication for stronger levels of protection.
No matter the device, user or login context, Okta Adaptive MFA and YubiKey together deliver a more reliable, compatible, and modern approach to strong authentication.

Accelerate Your Zero Trust Strategy with Strong Authentication
While the concept of Zero Trust has been a topic of conversation for a while, it is only recently that the conversation has shifted to how Zero Trust still means different things to different people. There may be many roads to cutting across the network, identity, and access control, and the array of definitions or ways to get there are dizzying.
Take a look at this whitepaper which will cover how to cut through all the noise when it comes to the Zero Trust framework and how an organisation should trust no individual or thing unless properly verified before being given access to the network and data.

Phoenix Software Protects the Public Sector Supply Chain With YubiKeys
Phoenix Software enables digital transformation in the workplace, empowering UK organisations to innovate and transform with cloud technology, data, AI, security, and collaboration tools. By understanding the individual goals of its customers, Phoenix delivers strong, outcome focused IT solutions and services that allow UK organisations to make a difference to the lives of their employees, service users, and communities. As a reseller with direct access to customers’ IT systems, Phoenix is part of the supply chain, which means the company has an important role in protecting critical infrastructure—not just by offering clients high-assurance security services, but also by securing its own IT infrastructure.
Customer Feedback
Millions of users across over 160 countries use Yubico to secure their stakeholder’s privacy and data.

Google defends against account takeovers and reduces IT costs
Mayank Upadhyay, Director of Security Engineering | Google Inc.
“We believe that by using this token we’ve raised the standard of security for our employees beyond what was commercially available.”

Making security effortless for employees
John “Four” Flynn, Information Security Manager | Facebook Inc.
“Protecting against remote attackers is a constant challenge, because once they gain access, they can move laterally through the organisation.”

Uk residents enjoy secure online access to government services
Marcel Wendy, Chief Technology Officer | GOV.UK
“We are pleased to partner with Yubico, a driving contributor of the FIDO U2F standard, to make this happen.”
Request a demo
Ready when you are! Take a quick demo with one of our experts and learn why millions of people rely on Yubico
to securely connect to the technologies that let them do their most important work.